The Cone of Silence: Easy email security.
-
The Cone of Silence requires a web browser that supports JavaScript and JavaScript must be enabled.
-
Save this document to your disk in Source format so you can use it later by opening the file in your browser.
-
Send a copy of this file to your friends so they can decode your messages, or direct them to this web page.
-
To decode a message you have received, copy the code text from the message to the Coded Text box and press the Decode button to make plain text above.
-
You can make your own code by making a simple change to this file using a text editor. See the comments in the JavaScript code for instructions.
How secure is The Cone of Silence?
The code is easy to crack but it protects against the most common threats such as casual viewers and automated scanners.
For example, a credit card thief may be using a tool like a search engine to scan email messages for key words like 'Visa', 'Mastercard', or 'American Express'. The Cone of Silence will foil such an attack.
Another example: Where I work, the automated email scanners won't let you use the word "naked", as well as many other common words, in an outgoing email. Using The Cone of Silence gets you past the automated scanner.
You could use ROT-13, and achieve about the same results, with a more common code, but that is even easier to decode.

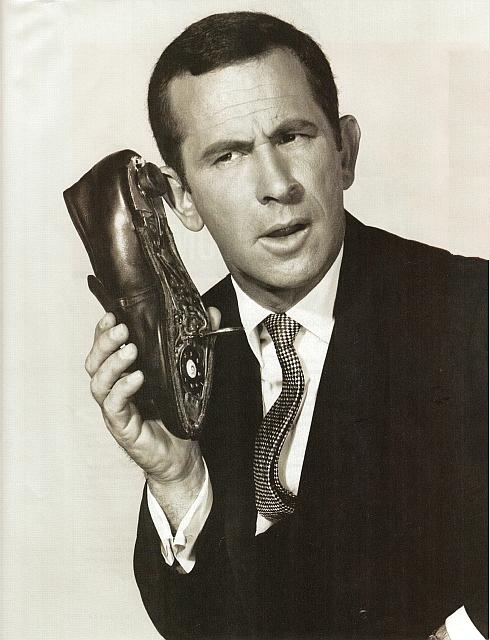
MAX: Chief I think we need to use
The Cone of Silence. CHIEF: Not The Cone of Silence Max.
MAX: It's the rules Chief.
CHIEF: Very well Max,
The Cone of Silence...
-- from the TV show 'Get Smart'.
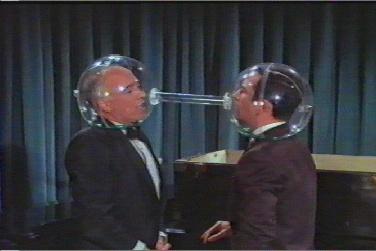
MAX: What did you say?
CHIEF: What?
MAX: What?
CHIEF: What?...